Money laundering is a serious continuous issue for companies. The issue continues to persist in 2025. Money laundering hides the illegal origin of funds; the UNODC states that it often impacts 2 to 5% of global GDP, or $800 billion to $2 trillion yearly. In this blog post, we’ll be summarising the techniques used, risks, and detection strategies for companies looking to improve their compliance in 2025.
Common Money Laundering Techniques
We’ll be giving details of and explaining several techniques that are used in money laundering below.
Structuring (Smurfing)
Smurfing is the first technique we’ll talk about. This technique is done by breaking large amounts of money into smaller transactions. For example, rather than getting detected for making a $10,000 transaction, the fraudster will send payments of $9,900. Things to watch out for with this category is small transactions that are done frequently, the use of multiple accounts or branches to make deteching more difficult, and unusual patterns that is shown by the individual or company.
Trade-Based Money Laundering (TBML)
The second technique we’ll explain to our readers is trade based money laundering, also known as TBML. With this technique, launderers exploit trade processes by not invoicing the correct amount, going under or over; creating phantom shipments for further launder money; or duplicating invoices. Import and export firms, freight forwarders, and luxury goods traders especially need to be careful with this technique. According to the U.S. Government Accountability Office (GAO), TBML accounts for the majority of illicit financial flows globally, with one estimate suggesting that it accounts for approximately 80% of illicit flows worldwide.
Real Estate Laundering
This technique is the buying or selling of properties to move or disguise funds from regulatory bodies. This is done by making cash deals, creating shell companies, undervaluing or flipping properties. Things you should look out for are price mismatches across different sources, rapid resales that are not normal, and complex ownership structures.
Casino and Gambling Laundering
This money laundering technique is done by using chips or online platforms in order to clean illicit cash. They do this by gambling a small amount to now draw attention to themselves. Another way is by using online casinos to get away with their financial crimes more quickly. They also use prepaid cards to not get caught. Using different aliases and user names across transactions and visiting different sites or counters to cash chips in and out are things to look out for when investigating this technique.
The hardest part of dealing with this technique is the loopholes there are in global gambling regulations.
Crypto-Based Money Laundering
Another technique we’ll talk more about with our readers is money laundering that is done using crypto. Since crypto is newer, it is easier to do transactions of anonymous and global kind using it. Fraudsters achieve this by using mixers, which collects all coins you possess and shuffless them randomly to different wallets you have. This is done to confuse compliance officers and other officials who are investigating transactions of every kind.
Another thing they do this kind of money laundering is by chain-hopping between different cryptocurrencies to create opportunities for hiding their transactions in less regulated options, and officers struggle to follow these long chain of transactions all the way.
Privacy coins like Monero help with anonymity as you can tell from its name. With these privacy coins hiding wallet addresses and transaction details, people who want to commit financial crimes are moving their funds around easier. Decentralised finance (DeFi) tools have less compliance checks, so this is dangerous as well. The lack of global regulation that is currently going on with crypto makes tracing done by compliance officers and other officials more difficult.
Shell Companies and Trusts
Now, let’s move onto another type of money laundering technique used by fraudsters. Shell companies and trusts are used since they are entities that have no real operations; so, these companies are effective since they conceal ownership details and don’t disclose the source of funds.
How can you tell that there is money luandering going on with this technique? The first thing to look out for is offshore setups in jurisdictions that are unknown. This helps them with anonymity. Layered ownership is another way they choose; they do this since having different owners that hide the beneficial owner slows down the investigation process and makes it harder to figure out money laundering is happening in the first place.
You can also tell that these are shell companies that probably commits money laundering crimes by them having no employees or physical office.
Prepaid Cards and E-Money Laundering
Prepaid cards or gift cards are effective tools that fraudsters use since these cards offer no details of the owner, giving them more anonymity. Another reason they use these cards is since it helps them achieve fast use during international payments.
These cards are risky since they have weak KYC compliance, there isn’t a way to regulate these cards that are without owner details. Another risk is crypto purchases, we’ve talked above about how crypto purchases that are done with prepaid cards are harder to trace back and used frequently when money laundering. If transactions of high amounts are done with these prepaid cards, it is another indicator of money laundering. If someone is using many prepaid cards for their transactions, this should be our readers’ first warning towards this consumer. If the transactions are done in, towards or from regions that are deemed higher risk, it is a sign for you to pay more attention to this customer or entity.
Invoice and Loan Fraud
When doing transactions, fraudsters who use this way put in fake loans or invoices to be able to explain their illicit transfers. We’ll explain more of this technique to our readers. This way is used heavily in trade finance, SME lending, and B2B transactions. Why so? The transactions that are done towards these companies or in these sectors naturally involve higher amounts of money, which makes it perfect for fraudsters to hide illicit funds.
They money launder using this way by inflating their invoices, or hiding dirty money as loan proceeds. These transactions give these fraudsters a legitimate paper trail for hiding their illicit funds until they are investigated by compliance officers and alike.
Charities and Non-Profit Abuse
Charities and non-profit organisations have long been known for being used in money laundering. We’ll give more details about this technique to help our readers inform themselves about money laundering tactics which might harm their companies.
This tactic is done by using these charities and non-profit organisations as a mask for hiding illegal flows. They might do this by creating fake donation paths or donating to organisations in areas that are of higher risk. Transactions of these kinds done towards charities and non-profit organisations with good thoughts in mind can be an efficient area for fraudsters to abuse since these transactions are done in a area that has limited oversight.
Which Industries Are Most Vulnerable to Money Laundering?
In this part, we’ll talk about the sectors which are the most vulnerable to financial crimes like money laundering because of several reasons like transaction amounts, anonymity chances, or regulatory gaps. Industries like real estate, casinos, art and luxury goods, cryptocurrency firms are the top industries that get affected by money laundering cases.
To avoid elevated risks because of the sector your company operates in, we advise our readers strong AML controls that ensure compliance.
What Is the Difference Between Terrorist Financing and Money Laundering?
We’ll give more details about the difference of two crimes, terrorist financing and money laundering. Money laundering is done by hiding the source of illicit funds; but, terrorist financing mainly involves legal funds that are then used for illegal purposes.
Money laundering is driven by the need for making profit, whereas terrorist financing is done with the purpose of benefiting certain ideologies in mind. Because of these differences, money laundering is dealt with by complying to AML compliance regulations while terrorist financing is fought by following CTF compliance regulations instead.
Emerging Money Laundering Techniques in 2025
We’ll talk more about 2025 money laundering tactics that are on the rise. The first is AI generated synthetic IDs; these IDs help disguise transaction details by making sure they are not verified. Another way is money laundering done using Metaverse assets, the increase of NFT popularity can be related to this technique.
One other technique used by fraudsters is in-game microtransactions. When considering how big the gaming industry is, this technique getting popular is no surprise. Finally, the last money laundering trend we’ll mention is exploiting central bank digital currencies (CBDCs) in early stages. Since these are newer in comparison, fraudsters are more easily finding regulatory loopholes and gaps before better regulations are implemented.
How to Detect and Prevent Money Laundering Techniques
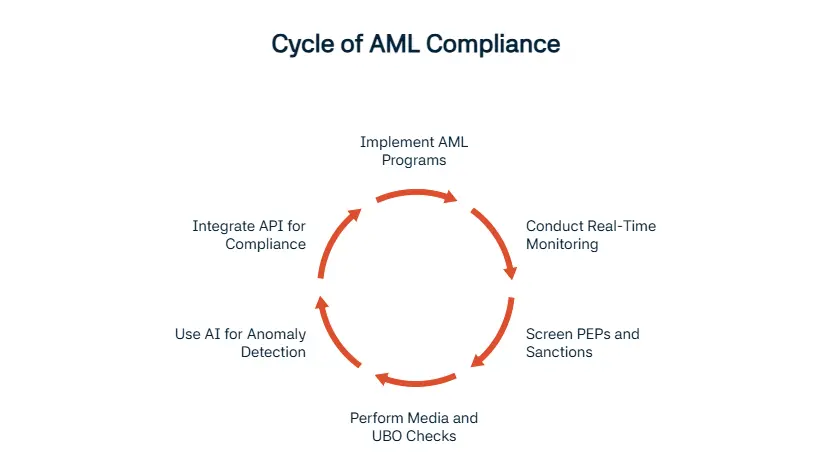
Since we’ve mentioned how many techniques money laundering involves, you might be needing more help with making sure your company is in compliance with AML, KYC, and CFT regulations. There are several ways of detecting and preventing money laundering from happening.
The first method we’ll mention is using AML programs that work with the risk based approach (RBA). This makes sure that you spend your company’s time and resources according to the entity’s risk score; a risk based approach is more efficient like this. Another way you can make sure you are in compliance with AML at all times is real-time monitoring and alerts. These will make sure that you are ready whenever with continuous monitoring that can then instantly alert the authorities if something suspicious is detected.
One other method is politically exposed persons (PEP) and sanctions screening. These are crucial since they are the main elements that is needed for reaching AML compliance. Another thing that helps is adverse media and ultimate beneficial owner (UBO) checks that help reach negative news about the entity or person and act accordingly. Finally, AI based anomaly detection is needed since these tools and programs need to evolve with the ever changing technologies. AI will help you protect your company.
One company that is helping you do these and many more is Sanction Scanner. Our experts at Sanction Scanner will assist you with instant risk screening. We are also using behaviour-based monitoring with API integrations that make sure your company gets its compliance needs met with ease.
FAQ's Blog Post
Criminals use placement, layering, and integration, and we recommend knowing these basics to stay compliant.
Layering hides the source by moving money around, and we suggest real-time monitoring to detect it.
Shell companies disguise true ownership, and we advise using KYB checks to reveal real owners.
Criminals manipulate invoices and pricing, and we recommend strong trade compliance controls.
Criminals use crypto for anonymous transfers, and we suggest adopting crypto AML tools.
Smurfing splits large sums into small deposits, and we recommend transaction monitoring to catch it.
Businesses protect themselves with CDD, monitoring, and training, and we suggest making compliance a daily habit.